This is a brief explainer of SSL certificates for anyone who’s curious. Content warning; there’s lots of acronyms when it comes to understanding internet traffic.
HTTP Protocol
When you hit a website/server you use a protocol called HTTP (Hypertext transfer protocol). This protocol opens up a connection with a server and can pass stuff like HTML (Hypertext Markup Language) to your web browser (client). Or this protocol can return data (often in JavaScript Object Notation – JSON or Extensible Markup Language – XML format) from an Application Programming Interface – API call. API responses such as 200 ok and 418 – “I’m a teapot” are HTTP responses.
One of the issues with using plain HTTP, is anyone can intercept that traffic and read everything in plain text. They can even introduce HTTP redirects so all of your information gets sent to their malicious server instead.
Introducing the secure layer (SSL)
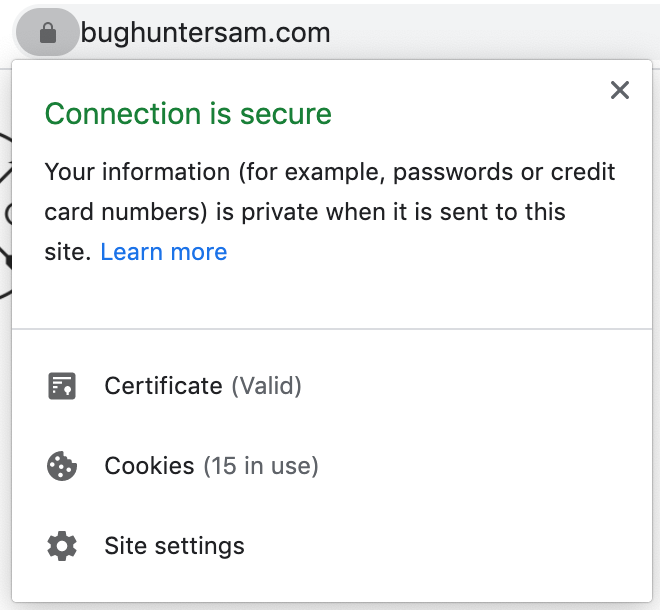
This is where HTTPS comes into to play. The S stands for Secure. By default, most web browsers these days use HTTPS and will let you know if the website you are accessing doesn’t use HTTPS. This is often done using Secure Socket Layer (SSL) and encryption.
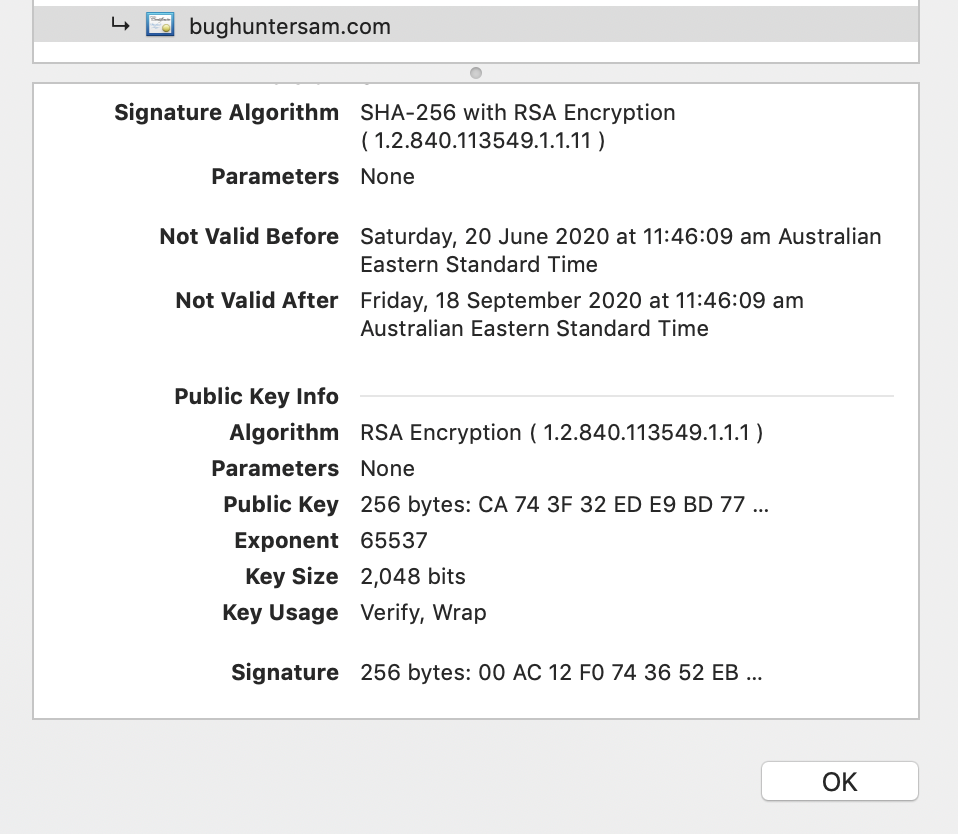
An SSL certificate is issued by trusted third party provider. This certificate comes with a public key and a private key. I use the private key on my server to encrypt data before I send it to your web client. Your web client then uses the public key to de-crypt the data.
My blog uses a self renewing certificate generated from Let’s Encrypt. And you can see this little lock icon in your browser to trust me. My website is legit, mate.
You can check out my certificate details, including details of when it expires and the public key information:
Expired SSL certificates
On my old blog, I use to purchase a SSL certificate from a certificate issuing authority, and manually upload it to my blog. This wasn’t hard, but I’d often have periods of my website having an expired SSL cert cause I was too lazy to upload it. If you go to my old blog today you get this SSL warning:
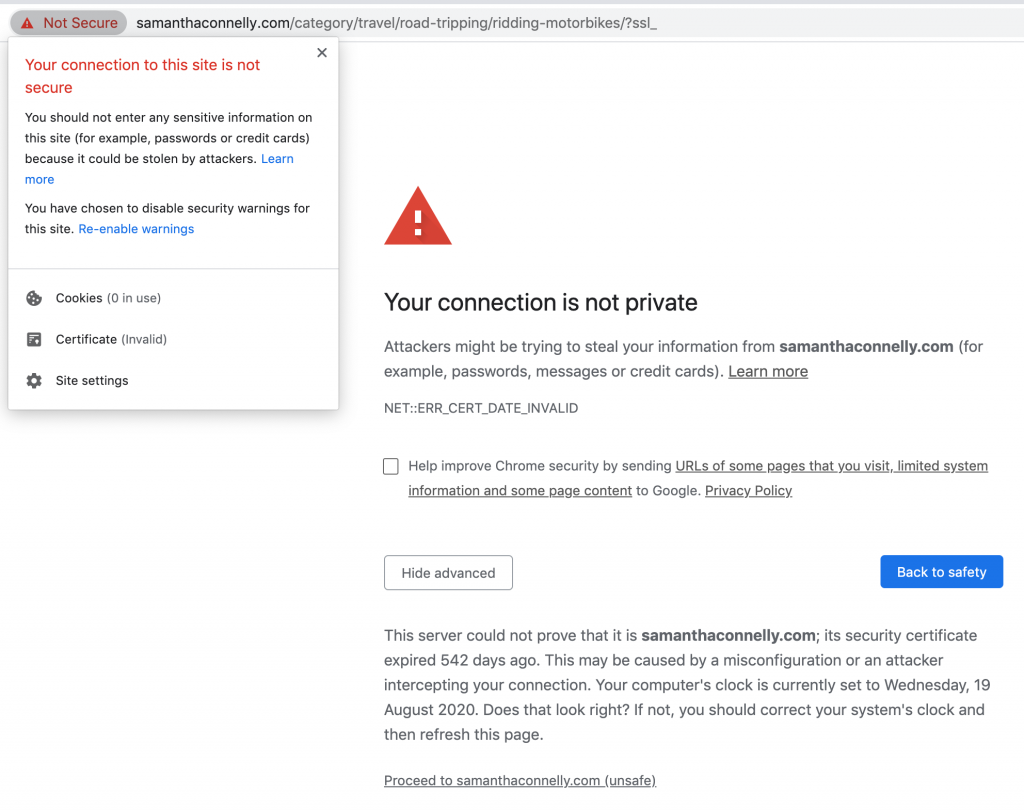
Also when you go to many internal test environments you get a similar warning, because teams often use self signed certificates to encrypt their internal test environment traffic.
Anyway, SSL stuff can get pretty complicated.I hope you learned something new or were able to refresh your SSL knowledge.
2 comments